Lifting the Fog – Part 5: Security of Embedded Systems relies on Teamwork
Modern embedded systems are more secure than ever.
They boot from verified code, rely on cryptographic trust chains, and are built on hardware designed with security in mind. And yet, cybersecurity incidents still happen, not because the technology is missing, but because security does not stop at a single component or company.
In today’s connected world, embedded systems are rarely built in isolation. They are the result of complex ecosystems involving hardware vendors, software suppliers, system integrators, and operators. Each contributes to a piece of the overall security posture.
The EU Cyber Resilience Act makes this reality explicit. Cybersecurity is not the responsibility of one player alone. It is a shared obligation across the entire lifecycle of a product.
Looking Back: From Foundations to Collaboration
Over the previous parts of Lifting the Fog, we have gradually uncovered what cybersecurity means for embedded systems. We started with the motivation behind regulations such as the Cyber Resilience Act, explored core concepts like the CIA Triad and cryptography, examined the convergence of IT and OT, and most recently defined the Root of Trust.
Together, these topics show that technical measures such as secure boot, signed firmware, and hardware-based trust are essential. At the same time, they reveal a clear limitation: technology alone cannot deliver compliance or long-term resilience.
This is where teamwork becomes critical.
What the Cyber Resilience Act Really Demands
The Cyber Resilience Act does not prescribe specific technologies. Instead, it defines outcomes. Products must be secure by design and by default. Vulnerabilities must be handled responsibly. Cybersecurity must be maintained throughout the entire product lifecycle.
For embedded systems with long lifetimes and complex supply chains, this has far-reaching implications. Responsibilities must be understood. Interfaces must be defined. Security must be treated as an ongoing process rather than a one-time feature.
Cybersecurity becomes a system-level discipline.
The House of Cyber Security: Giving Structure to Shared Responsibility
To make shared responsibility tangible, congatec uses the concept of the House of Cyber Security. It is not a single product or a checklist. It is a framework that illustrates how technical building blocks and organizational processes fit together.
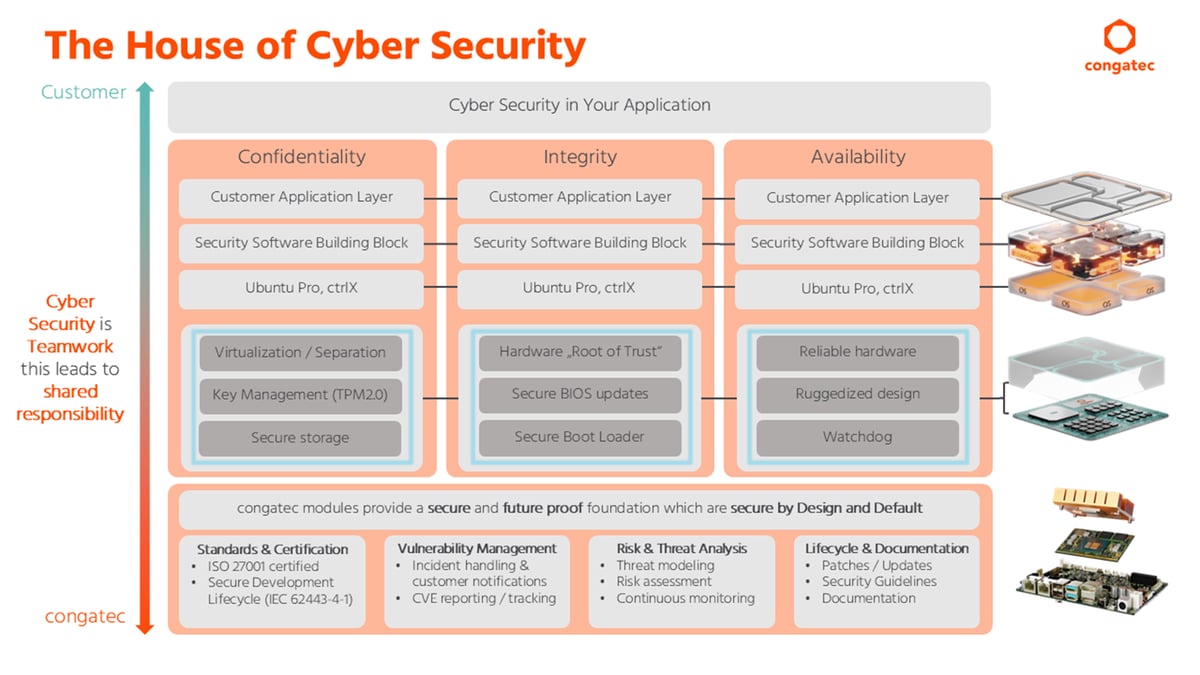
The Roof: Cyber Security in Your Application
At the top of the house sits the customer application. This is where cybersecurity requirements ultimately become visible, for example secure communication, protected data, and reliable operation in the field. The roof represents the outcome that users and operators experience. It depends entirely on the structure beneath it.
The Pillars: Confidentiality, Integrity, Availability
The house is supported by three pillars that span all layers of an embedded system.
- Confidentiality ensures that data is accessible only to authorized parties. This is supported by isolation mechanisms, secure storage, and key management.
- Integrity ensures that software and firmware remain authentic and untampered. This relies on Roots of Trust, secure boot mechanisms, and signed updates.
- Availability ensures that systems continue to operate reliably, even in demanding industrial environments, supported by robust hardware design and monitoring mechanisms.
No single layer can uphold these pillars on its own. They emerge only when hardware, firmware, software, and applications work together.
The Core: Secure by Design and by Default
At the heart of the house are modular embedded building blocks, or Computer on Modules. These provide a secure and future-ready foundation. Hardware-based Roots of Trust, support for secure boot, optional TPM integration, and industrial grade reliability form a baseline that customers can build upon.
This foundation does not remove responsibility from customers. Rather, it helps simplify system design, reduce risk, and align products with the secure-by-design expectations of the Cyber Resilience Act.
The Ground Floor: Processes That Sustain Security
Cybersecurity does not end when a product is shipped. That is why the house stands on four essential process elements.
- Standards and certification to support secure development practices
- Vulnerability management to address incidents, track vulnerabilities, and communicate transparently
- Risk and threat analysis to continuously assess evolving attack vectors
- Lifecycle and documentation to support updates, patches, and long-term maintenance
These elements ensure that cybersecurity remains effective over years, not just at first boot.
Lifting the Fog Together: Cyber Security Is Teamwork
Across the entire house, one message remains consistent: cybersecurity is teamwork and therefore a shared responsibility. The Cyber Resilience Act formalizes this reality. Cybersecurity for embedded systems starts at the root, but it grows through collaboration. This means hardware vendors, software providers, system integrators, and operators all play a role.
Clear structures and clearly defined interfaces help ensure that responsibilities are understood and that security gaps are avoided. By combining strong technical foundations with structured processes and shared responsibility, complexity becomes manageable and regulatory requirements become achievable.
But the journey does not end here.
The EU Cyber Resilience Act is not a static milestone. It is a long-term framework that will shape how embedded products are designed, maintained, and evolved over many years. Understanding the principles is the first step. Applying them in real projects is the next. Stay tuned to our blog page for an upcoming post about the modular path to CRA compliance.
Related Content
In the meantime, read “Three Dangerous Misconceptions About the Cyber Resilience Act” to avoid common pitfalls that could undermine your CRA compliance efforts.